Send OTP -Best Practices For Two-Factor Authentication
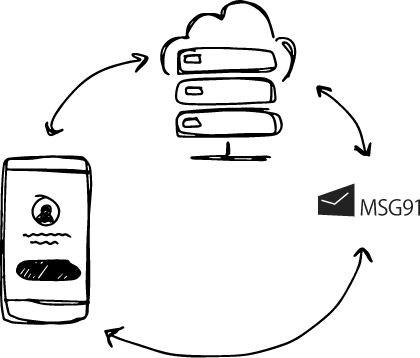
How does OTP work?
The ability to perform financial transactions on-the-go is a real blessing in today's world. And with every progressive step in technology, comes a concern of security and dependability. This becomes all the more worrisome in the case of theft of credit/debit cards and other account details. Enter OTP, a simple solution to a rather dangerous threat.
 Mobile number verification, 2-factor login, voice backup call,OTP protected transactions with enhanced security and speed.
Mobile number verification, 2-factor login, voice backup call,OTP protected transactions with enhanced security and speed.
What is OTP Code?
OTP (one-time-password) comes as a saviour, acting as a barrier of protection that authenticates the transaction. The OTP process involves the generation of a random six-digit code by the application/website, which is sent to the user's registered mobile number, for them to enter the portal and authenticate themselves.
Sounds like a cakewalk, doesn’t it?
But, there was a time when one-time-passwords were notorious in India for delays or non-delivery with a lot of users unable to receive OTP and "OTP verification failed" errors
Failed OTP can be frightening, simply because all it takes for a user to leave a website is 8 seconds!
Sensing this big gap in the market for high-priority SMS or what we call OTP, we grabbed the opportunity with both hands and voila ‘SendOTP’ was conceived and yes, we did make it a cakewalk.
The OTP process itself is quite simple, but some of the challenges it faces, like poor connectivity and undelivered messages led us to conceive and develop MSG91 SendOTP which deals with 'high-priority SMS'. Through this solution, we generate and route messages through a separate high-priority channel.
Conceiving it was simple, but it was the execution and development of a fool-proof product that was challenging. We wanted to give our users a comprehensive solution to the persisting problem of delays and non-delivery and equally important, authenticating the user through a platform that was easy-to-use. A platform where we generate and deliver OTP to your clients through a dedicated high-priority route!
After many arguments, much discussion and many failed attempts, MSG91 SendOTP arrived with a promise. A promise of
- Guaranteed delivery of OTP
- Make the integration of 2FA (two-factor authentication) easy for developers
- Reduce the infrastructure cost involved in the process
- Provide the best security for the user
Welcome to SendOTP, your one-shot OTP!
A one-time-password generating, delivering and verifying mechanism that by simply copy-pasting a couple of codes allows users to integrate the two-factor authentication and everything from generating, delivering and verifying the one-time-password is done by SendOTP (remember we said cakewalk).
2FA Services by MSG91
But what makes SendOTP stand out is not its simplicity, but it being foolproof from day one – a Voice Call backup, so there’s no need for a Plan B. Also, did we mention the Voice Call comes at no extra cost. You got that right, in the event of non-delivery via text SMS we send a Voice Call and that too at our own expense.
 We understand you do recognize the importance of such a unique feature but again, it’s our responsibility and sometimes our pride where we need to tell you (and not boast) the importance of that Voice Call backup.
We understand you do recognize the importance of such a unique feature but again, it’s our responsibility and sometimes our pride where we need to tell you (and not boast) the importance of that Voice Call backup.
Another privilege of using SendOTP, the times when the government is forced to ban bulk messaging, instant messaging and mobile Internet in various parts of the country.
Due to the ban, internet-based businesses face disruption in their day-to-day communication with customers. Banking sector and internet-based enterprises are worst-hit as their transactions become incomplete without OTP verifications, and a ban on bulk SMS service leaves them fidgeting.
SendOTP has time and again with its Voice Call backup bridged the communication gaps between customers and enterprises by offering Voice OTP, in the wake of the ban on delivery of text OTP, allowing us to serve our customers even during times when it seems highly impossible.
But that’s not it…
We envisioned a comprehensive solution for 2FA and we give our users all that and more with
- OTP Engineering
- Voice Call Backup
- Global Coverage
When the customer asks for OTP and if the same is not delivered within 30 seconds, it is automatically sent via a call. And it works every single time. This solution with complete reporting is available and ready to implement in just a few minutes.
Your OTP will never fail; come what may, because yes, all it takes for a user to decide and leave your website is 8 seconds.
SendOTP has time and again with its voice call backup bridged the communication gap between customers and enterprises by offering Voice OTP, allowing us to serve our customers even during times when it seems highly impossible.
How to choose your OTP provider
Today, as online transactions have become the order of the day, there are plenty of providers for businesses to choose from. Here are a few tips on how to choose the most suitable provider:
- Do your research: While it is common advice to go by referrals, it is best to do your due diligence and find the right provider for you. Here the internet would be your best friend to find high-priority SMS providers. However, make sure to pay attention to client feedback, as that will help you get a clear picture.
- Check pricing details: While choosing a provider for different types of OTP, it is important to check and analyse their price plans. The nature of the service usually comes with a money-back guarantee, which is a factor that will help make your decision.
- Technical infrastructure: As in the case of any other provider, make sure your OTP high-priority SMS provider has the technical abilities to deal with different types of SMS, and also has the sound infrastructure to execute these types of SMS in bulk.
MSG91 ticks all the above boxes ensuring your customers experience a hassle-free transaction 24x7. Reach out to us for a free demo.
- send-otp
Copyright 2008-2025, Superheroes, Inc. | All rights reserved.